You’ve built your website, invested time and resources, and established an online presence. Now, it’s time to ensure its longevity and integrity. Your WordPress website, like any digital asset, is a potential target for malicious actors. This guide provides a comprehensive approach to securing your site, outlining practical steps and preventative measures to safeguard against common threats.
Before you can effectively defend your website, you need to understand what you’re up against. The threats targeting WordPress sites are diverse and constantly evolving.
Common Attack Vectors
Hackers utilize various methods to exploit vulnerabilities. Familiarizing yourself with these helps you anticipate and counter them.
- Brute-Force Attacks: These involve automated attempts to guess your login credentials. Bots repeatedly try different username and password combinations until they find a match.
- SQL Injection: If your website uses a database (which WordPress does), attackers might try to insert malicious SQL code into input fields to manipulate or extract data.
- Cross-Site Scripting (XSS): This attack injects client-side scripts into web pages viewed by other users. This can lead to session hijacking, defacement, or data theft.
- Malware Distribution: Compromised sites are often used to host and distribute malware, infecting visitors’ computers and further spreading malicious code.
- Denial-of-Service (DoS) and Distributed Denial-of-Service (DDoS) Attacks: These attacks overwhelm your server with traffic, making your website unavailable to legitimate users.
- Phishing: Attackers might create fake login pages or emails to trick you or your users into revealing credentials.
- Insecure Plugins and Themes: Outdated or poorly coded plugins and themes can introduce backdoors and vulnerabilities that hackers exploit.
- Zero-Day Exploits: These are vulnerabilities that are unknown to the software vendor and, therefore, no patch exists. While less common, they are highly dangerous.
Motivations of Attackers
Understanding why attackers target websites can provide context for the security measures you implement.
- Financial Gain: This is a primary motivator. Attackers may steal credit card information, extort money, or use your site for cryptocurrency mining.
- Data Theft: Personal information, customer databases, and intellectual property are valuable assets.
- Reputation Damage: Competitors or disgruntled individuals might attempt to deface your website or spread misinformation.
- Malware Propagation: Your site might be used as a stepping stone to infect other systems or build botnets.
- Website Defacement: Some attackers simply aim to assert their presence or spread a message by altering your website’s content.
- Access to Server Resources: Your server’s processing power and bandwidth can be exploited for sending spam, hosting illicit content, or launching further attacks.
In addition to the comprehensive WordPress Security Guide to Protect Your Website from Hackers, it’s also beneficial to stay informed about the broader implications of online presence and investment trends. For instance, you might find the article on the resale value of PK domains insightful, as it discusses investment trends and predictions for 2025. Understanding the value of your domain can play a crucial role in your overall website strategy. You can read more about it here: the resale value of PK domains.
Fortifying Your WordPress Core
The foundation of your website’s security lies in the WordPress core files, database, and configuration. Neglecting these fundamental aspects leaves your site vulnerable from the outset.
Staying Updated: The Cornerstone of Security
Outdated software is a principal cause of security breaches. Regularly updating your WordPress core, themes, and plugins is not optional; it’s imperative.
- WordPress Core Updates: WordPress development teams frequently release updates that include security patches for newly discovered vulnerabilities. Apply these updates promptly. Before a major update, consider backing up your site to prevent unexpected issues.
- Theme Updates: Just like the core, themes can contain security flaws. Use reputable themes and ensure they are maintained by their developers.
- Plugin Updates: Plugins expand WordPress functionality but are also common entry points for attackers. Prioritize updates for all installed plugins. Delete any plugins you no longer use.
Strong Authentication Practices
Weak credentials are an open invitation to hackers. Implementing robust authentication mechanisms significantly reduces the risk of unauthorized access.
- Complex Passwords: Enforce strong password policies. Require a combination of uppercase and lowercase letters, numbers, and symbols. Avoid common words or easily guessable sequences. Use a password manager to generate and store complex passwords.
- Unique Usernames: Do not use ‘admin’ as a username. This is the first username brute-force attackers will try. Choose less obvious usernames for all administrative accounts.
- Two-Factor Authentication (2FA): Implement 2FA for all administrative users. This adds an extra layer of security by requiring a second verification method (e.g., a code from your phone or a hardware token) in addition to the password. Numerous plugins are available for this purpose.
- Limit Login Attempts: Install a plugin that limits the number of failed login attempts. This mitigates brute-force attacks by temporarily blocking IP addresses that exceed a specified limit.
- User Role Management: Assign the lowest necessary privileges to each user role. For instance, content creators do not need administrator access. This limits the damage an attacker can do if a non-administrator account is compromised.
Database Security Measures
Your WordPress database stores all your content, user information, and settings. Protecting it is paramount.
- Change Default Database Prefix: During WordPress installation, you can change the default
wp_database table prefix. This makes it harder for automated SQL injection tools to target your tables. If your site is already live, there are plugins and manual methods to change this prefix, but proceed with caution and a backup. - Regular Database Backups: Implement a robust backup strategy that includes your database. In the event of a breach, you can restore a clean version of your site.
- Secure Database Configuration: Ensure your database user has only the necessary privileges. Avoid using
rootaccess for your WordPress database user.
Securing Your Server Environment
Your WordPress website resides on a server, and the security of that server directly impacts your site’s safety. Many of these points will apply whether you manage a dedicated server, a VPS, or shared hosting.
Web Hosting Provider Selection
The choice of your hosting provider is a critical security decision. A responsible host offers a foundational layer of protection.
- Reputable Host: Choose a hosting provider with a strong track record for security. Look for features like regular backups, firewalls, malware scanning, and prompt security incident response.
- Server-Level Security: Inquire about their server-level security measures, including DDoS protection, intrusion detection systems, and operating system patching schedules.
- Website Isolation: On shared hosting, ensure your site is adequately isolated from other clients’ websites to prevent cross-site contamination from a compromised neighbor.
- SSL/TLS Certificates: Ensure your host supports and facilitates the installation of SSL/TLS certificates. This encrypts data transmitted between your website and users’ browsers. Let’s Encrypt provides free SSL certificates, making this an accessible security measure. Configure your site to redirect all traffic to HTTPS.
File and Directory Permissions
Incorrect file and directory permissions are common security vulnerabilities, allowing attackers to modify or upload malicious files.
- Principle of Least Privilege: Grant the minimum necessary permissions.
- Recommended Permissions:
- Directories:
755(rwxr-xr-x) – Owner can read, write, and execute; group and others can read and execute. - Files:
644(rw-r–r–) – Owner can read and write; group and others can only read. wp-config.php:600or400– This file contains sensitive database credentials. Restricting access to only the owner (the web server user) is crucial.- Regular Audits: Periodically check your file permissions to ensure they haven’t been altered.
Hardening wp-config.php and .htaccess
These are two of the most powerful and therefore most sensitive configuration files in your WordPress installation.
- Move
wp-config.php(for advanced users): While controversial and not universally recommended for every setup, movingwp-config.phpone directory above the WordPress root can, in some server configurations, prevent direct access if the web server configuration is compromised. This requires careful .htaccess or NGINX configuration. - Authentication Keys and Salts: Ensure
wp-config.phpcontains unique and long authentication keys and salts. These encrypt cookie information, making session hijacking more difficult. If you haven’t generated these during installation, you can do so using the WordPress API and update yourwp-config.phpfile. - Disable File Editing (WP_DEBUG): Add
define('DISALLOW_FILE_EDIT', true);to yourwp-config.phpfile. This prevents administrators from editing theme and plugin files directly from the WordPress dashboard, reducing the impact if an admin account is compromised. - Block XML-RPC: XML-RPC (
xmlrpc.php) is a legitimate WordPress feature but is frequently exploited for brute-force attacks and DDoS. If you don’t use it (e.g., for mobile apps or external publishing tools), disable it. You can do this via your.htaccessfile or with a security plugin.
“`apache
Block WordPress xmlrpc.php requests
Order Deny,Allow
Deny from all
“`
- Protect
wp-includesandwp-content: Add rules to your.htaccessto prevent direct access to sensitive files within these directories, especially PHP files. - Disable Directory Listing: Add
Options -Indexesto your.htaccessfile to prevent visitors from browsing the contents of your directories if anindex.phporindex.htmlfile is missing. This hides potential vulnerabilities and prevents reconnaissance.
Implementing Security Plugins and Tools
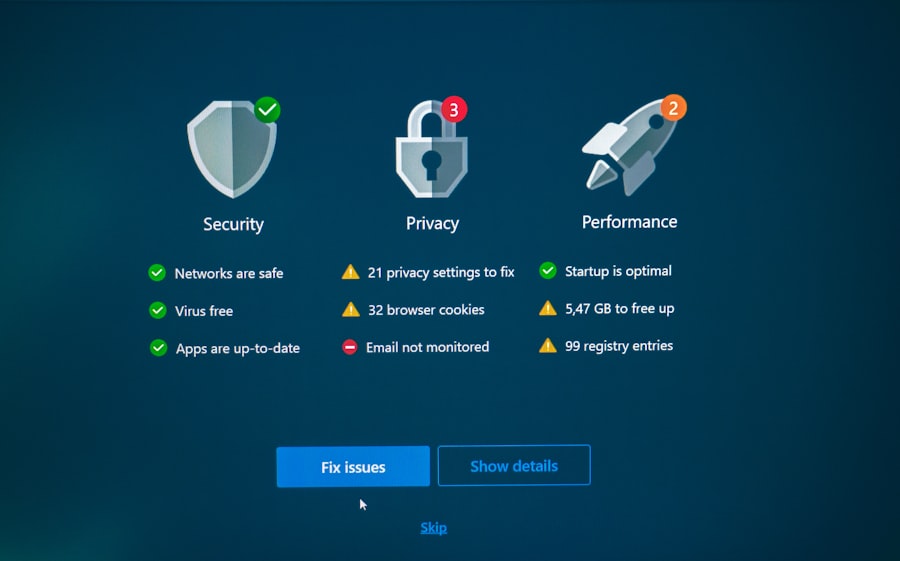
While manual configuration is essential, security plugins can automate many tasks, provide real-time monitoring, and offer advanced protection features.
All-in-One Security Solutions
These plugins offer a suite of security features to protect various aspects of your site.
- WordPress Security Plugins: Popular options like Wordfence Security, Sucuri Security, iThemes Security Pro, and WP Cerber Security provide firewalls, malware scanning, login attempt limiting, file integrity monitoring, and more. Carefully research and choose one that fits your needs and doesn’t conflict with other plugins.
- Firewalls (WAF – Web Application Firewall): A WAF filters malicious traffic before it reaches your WordPress application. Some security plugins include WAF functionality, while others are external services. A WAF can block common attack patterns, brute-force attempts, and known malicious IPs.
- Malware Scanners: These inspect your files and database for malicious code, backdoors, and common malware signatures. Schedule regular scans and address any reported issues promptly.
Backup and Restoration Solutions
A robust backup strategy is your last line of defense against data loss due to hacking, server failure, or accidental deletion.
- Automated Backups: Implement automated, scheduled backups of your entire website (files and database). Store these backups off-site (e.g., cloud storage like Dropbox, Google Drive, Amazon S3) to prevent loss if your server is compromised.
- Multiple Backup Points: Maintain multiple backup versions (e.g., daily, weekly, monthly) to ensure you have a clean restore point should an issue go unnoticed for a period.
- Test Restorations: Periodically test your backup restoration process in a staging environment. This verifies that your backups are viable and that you can successfully restore your site if required. This practice is often overlooked and can lead to panic during a real incident.
- Dedicated Backup Plugins: Plugins like UpdraftPlus, BackWPup, or VaultPress (now Jetpack Backup) offer comprehensive backup solutions with various storage options and scheduling capabilities.
Security Enhancements for Specific Threats
Beyond general security, target specific threats with dedicated tools.
- Spam Protection: Use anti-spam plugins like Akismet or reCAPTCHA to prevent comment spam and contact form abuse, which can sometimes be used for injecting malicious links.
- Bot Protection: Implement CAPTCHA or other bot detection mechanisms on login pages and comment forms to deter automated attacks.
- HTTP Security Headers: Configure security headers (like Content Security Policy, X-XSS-Protection, X-Frame-Options) via your
.htaccessor server configuration. These headers instruct browsers on how to behave when interacting with your site, mitigating various client-side attacks.
To enhance your website’s performance while ensuring its security, you might find it beneficial to explore strategies for optimizing speed and user experience. A related article that delves into this topic is available at Mastering Core Web Vitals, which provides insights on how to improve your WordPress site’s loading times and overall functionality. By combining security measures with performance enhancements, you can create a robust online presence that not only protects against hackers but also offers a seamless experience for your visitors.
Ongoing Maintenance and Monitoring
| Security Measure | Description |
|---|---|
| Use Strong Passwords | Encourage the use of complex passwords with a combination of letters, numbers, and special characters. |
| Keep WordPress Updated | Regularly update WordPress core, themes, and plugins to patch security vulnerabilities. |
| Install Security Plugins | Utilize security plugins to add an extra layer of protection against common threats. |
| Enable Two-Factor Authentication | Require users to provide a second form of verification in addition to their password. |
| Backup Your Website Regularly | Implement regular backups to ensure that you can restore your website in case of a security breach. |
Security is not a one-time setup; it’s a continuous process. Vigilance and regular maintenance are crucial for long-term protection.
Regular Security Audits
Periodically review your website’s security posture to identify and address potential weaknesses.
- Plugin and Theme Audit: Regularly review your installed plugins and themes. Delete any that are unused, outdated, or from untrustworthy sources. Too many plugins can increase the attack surface.
- User Account Audit: Review all user accounts, roles, and privileges. Remove inactive accounts and adjust permissions as needed. Pay particular attention to administrator accounts.
- Configuration Review: Revisit your
wp-config.phpand.htaccessfiles to ensure all security measures are still in place and properly configured.
Monitoring for Suspicious Activity
Proactive monitoring allows you to detect and respond to security incidents quickly.
- Website Activity Logs: Monitor your server logs and WordPress activity logs for unusual login attempts, file modifications, or access patterns. Security plugins often provide consolidated activity logs.
- Uptime Monitoring: Use an uptime monitoring service (e.g., UptimeRobot, Pingdom) that alerts you if your website goes offline. This can indicate a DDoS attack or server compromise.
- Malware Scans: Schedule daily or weekly malware scans using your chosen security plugin or an external service.
- Google Search Console: Keep an eye on your Google Search Console account for security notifications. Google often detects malware or spam links on websites before site owners do.
- File Integrity Monitoring: Some security plugins monitor changes to your core WordPress files. If a core file is unexpectedly modified, it could indicate a compromise.
Incident Response Plan
Despite your best efforts, a breach can still occur. Having a plan in place minimizes damage and facilitates recovery.
- Backup Restoration: Your incident response plan should prioritize restoring from a clean backup.
- Isolate the Compromise: Immediately take the website offline or restrict access to prevent further damage and prevent the spread of malware.
- Identify the Cause: Investigate how the breach occurred. Review logs, scan for malware, and analyze recent changes to files or configurations.
- Clean and Secure: Remove all malicious code, update all software, change all passwords, and address the vulnerability that led to the breach.
- Notify Affected Parties: If customer data was compromised, you might have legal obligations to notify affected individuals.
- Learn from the Incident: Analyze what went wrong and implement additional security measures to prevent similar incidents in the future.
Educating Yourself and Your Team
Technology evolves, and so do security threats. Continuous learning is a vital part of maintaining a secure online presence.
Stay Informed
Keep abreast of the latest WordPress security news and developments.
- Official WordPress Security Advisories: Follow official WordPress security announcements.
- Security Blogs and Resources: Subscribe to reputable cybersecurity blogs and news sources that cover WordPress-specific threats and vulnerabilities.
- Plugin and Theme Developer Announcements: Pay attention to security releases or vulnerability disclosures from the developers of your installed themes and plugins.
Best Practices for Content Creation and User Behavior
Your website’s users and content creators also play a role in its security.
- Educate Users on Password Hygiene: If you have multiple users, ensure they understand the importance of strong, unique passwords and 2FA.
- Review Submitted Content: If your site allows user-generated content, implement rigorous moderation to prevent the injection of malicious code or spam links.
- Avoid Suspicious Links and Downloads: Educate yourself and your team about phishing emails and suspicious downloads that could compromise local machines, potentially leading to website access.
By systematically addressing each of these areas, you establish a resilient defense against the vast majority of threats targeting WordPress websites. Security is a journey, not a destination, requiring consistent attention and adaptation to the evolving digital landscape. Your commitment to these practices will significantly enhance your website’s integrity and protect your online assets.
FAQs
1. Why is WordPress security important for website owners?
WordPress is a popular platform for website creation, making it a prime target for hackers. Without proper security measures, websites can be vulnerable to attacks, leading to potential data breaches, loss of customer trust, and damage to the website’s reputation.
2. What are some common security threats to WordPress websites?
Common security threats to WordPress websites include brute force attacks, malware injections, SQL injections, and cross-site scripting (XSS) attacks. These threats can compromise website functionality, steal sensitive information, and damage the website’s reputation.
3. What are some best practices for securing a WordPress website?
Some best practices for securing a WordPress website include keeping the core software, themes, and plugins updated, using strong and unique passwords, implementing two-factor authentication, using a reputable web hosting provider, and regularly backing up website data.
4. How can website owners protect their WordPress website from hackers?
Website owners can protect their WordPress website from hackers by using security plugins, implementing a web application firewall, limiting login attempts, disabling file editing within the WordPress dashboard, and regularly scanning for malware and vulnerabilities.
5. What should website owners do if their WordPress website is hacked?
If a WordPress website is hacked, website owners should immediately take the website offline, change all passwords, restore the website from a clean backup, and conduct a thorough security audit to identify and address any vulnerabilities that may have been exploited by the hacker.









Add comment