You’ve poured your heart and soul into building your small business. You’re passionate about your product or service, and you’ve worked tirelessly to get it off the ground. Now, you’re ready to take the next crucial step: establishing an online presence. Your website is your digital storefront, your 24/7 salesperson, and often, the first impression prospective customers have of your brand. But as you embark on this exciting journey, a shadow looms: website security.
The thought of cyber threats might seem overwhelming, conjuring images of shadowy hackers and sophisticated attacks. Perhaps you’ve even told yourself, “I’m just a small business; who would target me?” The unfortunate truth is, even the smallest businesses are targets. In fact, small businesses are often seen as easier prey by cybercriminals because they may have fewer resources and less robust security measures in place. Ignoring website security is like leaving your physical store unlocked overnight – an invitation for trouble.
This guide is designed to demystify website security for you, the small business owner. You don’t need to be a tech wizard to understand and implement essential security practices. We’ll break down complex topics into manageable steps, empowering you to protect your online assets, your customer data, and your business’s reputation. By the end of this article, you’ll have a clear roadmap to building a secure foundation for your online endeavors. Let’s begin securing your digital future, one step at a time.
It’s critical to start by understanding why website security is not just a “nice-to-have” but an absolute necessity for your small business. You might believe you’re too small to be a target, but this couldn’t be further from the truth. Cybercriminals are often opportunistic, and their attacks aren’t always targeted at specific individuals or businesses. Instead, they look for vulnerabilities that are easy to exploit.
The Illusion of Anonymity
You operate a small business, perhaps serving a local community or a niche online market. It feels personal, intimate even. But online, anonymity can be a double-edged sword. While it can offer privacy, it also means your business footprint might seem less significant to you than it actually is to external observers.
Hackers Don’t Discriminate
Think of it this way: a burglar doesn’t just target mansions; they also look for unlocked doors and open windows in smaller homes. Cybercriminals operate on a similar principle. They scan the internet for websites that lack basic security defenses. Your website, regardless of its size, is a potential gateway.
Data is the New Gold
The data you collect, even if it seems mundane to you, can be incredibly valuable to others. This includes customer names, email addresses, phone numbers, and potentially even payment information if you process transactions on your site. This data can be sold on the dark web, used for identity theft, or leveraged for phishing scams.
Common Threats to Small Businesses
Understanding the types of attacks you might face will help you appreciate the importance of preventative measures. These aren’t abstract concepts; they are real dangers that can severely impact your business.
Malware and Viruses: Silent Saboteurs
Malware, or malicious software, can infect your website and cause all sorts of problems. It can steal data, redirect your visitors to malicious sites, display unwanted advertisements, or even hold your website hostage for ransom. A single piece of malware can spread like a virus, infecting your site and potentially your visitors’ devices.
Phishing and Social Engineering: Exploiting Trust
While these attacks often target your users directly, a compromised website can be used as a platform to launch phishing campaigns. Imagine your website being used to trick your customers into revealing their login credentials or personal information. This damages your brand’s reputation and erodes customer trust, which is incredibly difficult to rebuild.
Denial-of-Service (DoS) and Distributed Denial-of-Service (DDoS) Attacks: Shutting You Down
These attacks aim to overwhelm your website with traffic, making it inaccessible to legitimate users. Imagine your online store being flooded with so many fake visitors that no one can actually browse or purchase your products. For a small business, a prolonged or even a short DoS/DDoS attack can result in significant lost revenue and reputational damage.
Data Breaches: The Ultimate Nightmare
This is the most severe and damaging threat. A data breach occurs when unauthorized individuals gain access to sensitive information stored on your website or its associated databases. This can include customer lists, financial records, intellectual property, and more. The consequences can range from hefty fines to a complete loss of customer trust and a damaged brand image that takes years to repair.
SQL Injection: Manipulating Your Database
This is a common attack where an attacker inserts malicious SQL code into input fields on your website, such as search bars or login forms. If your website is not properly secured, this code can be executed by your database, allowing the attacker to view, modify, or delete your data.
By recognizing these threats, you move from a position of ignorance to one of informed caution. You understand that your website isn’t just a passive digital brochure; it’s an active participant in your business operations and a potential target. With this understanding, you’re ready to explore the foundational elements of protecting your digital asset.
For small business owners looking to enhance their website security, it’s essential to understand the broader context of web hosting options available to them. A related article that delves into a different aspect of web management is “What is Reseller Hosting and How Does It Work?” which provides valuable insights into how reseller hosting can be a viable option for those looking to manage multiple websites or offer hosting services to clients. You can read more about it by visiting this link: What is Reseller Hosting and How Does It Work?.
Building a Secure Foundation: The Essentials You Can’t Ignore
Before diving into advanced security measures, it’s crucial to ensure your website is built on a fundamentally secure foundation. Think of this as the structural integrity of your digital building. Without strong walls and a solid roof, no amount of security alarms will truly protect you.
Choosing a Reliable Hosting Provider
Your web hosting provider is the landlord of your website. They provide the server space and infrastructure where your website’s files reside. The security practices of your hosting provider directly impact your website’s security.
Shared vs. Dedicated Hosting: What’s the Difference?
- Shared Hosting: This is the most common and affordable option for small businesses. You share server resources with multiple other websites. While cost-effective, a security lapse on another website on the same server could potentially affect yours. It’s like living in an apartment building – the actions of your neighbors can sometimes impact your living situation.
- Dedicated Hosting: Here, you have an entire server exclusively for your website. This offers greater control and isolation, significantly enhancing security. However, it comes at a higher cost.
- Virtual Private Server (VPS) Hosting: This offers a middle ground, providing dedicated resources within a shared server environment. It offers more isolation than shared hosting but is generally more affordable than dedicated hosting.
Look for Security Features
When selecting a host, inquire about their security measures. Do they offer:
- Firewalls: Network security devices that monitor and control incoming and outgoing network traffic based on predetermined security rules.
- Intrusion Detection/Prevention Systems (IDS/IPS): Systems that monitor network traffic for malicious activity and can take action to block it.
- Regular Backups: How often do they back up your website? Are these backups stored securely and off-site?
- Malware Scanning: Do they proactively scan your server for malware?
- DDoS Mitigation: Do they have measures in place to protect against DDoS attacks?
Reputation Matters
Research reviews and testimonials about potential hosting providers. Look for providers with a strong track record in security and customer support. Don’t be afraid to ask questions about their security protocols before committing.
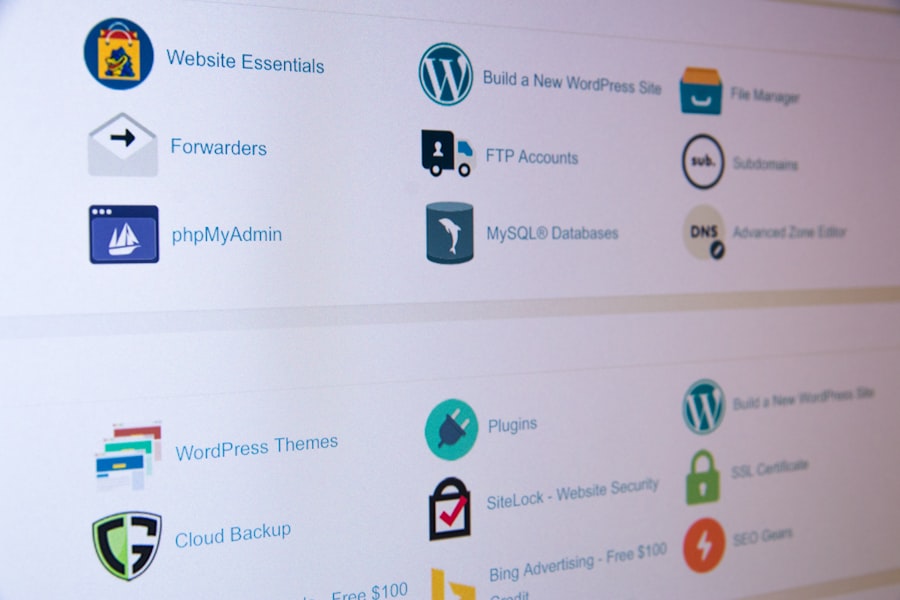
Secure Website Development Practices
The way your website is designed and coded plays a significant role in its vulnerability. Even if you use a content management system (CMS) like WordPress, WooCommerce, or Shopify, understanding these principles will help you work with developers or choose secure themes and plugins.
Keeping Software Up-to-Date: A Non-Negotiable
This is arguably the most critical aspect of website security. Developers continuously release updates to address bugs, improve performance, and patch security vulnerabilities. Outdated software is a gaping hole in your security defenses.
Content Management System (CMS) Updates
If you use a CMS like WordPress, Joomla, or Drupal, ensure the core software is always updated to the latest version. This is often a one-click process, making it incredibly easy to maintain a secure system.
Plugin and Theme Updates
Third-party plugins and themes are incredibly useful for extending the functionality and appearance of your website. However, they can also be sources of vulnerabilities. Always update your plugins and themes promptly once new versions are released. If a plugin or theme developer hasn’t updated their software in a long time, consider replacing it with a more actively maintained alternative.
Server-Side Software Updates
Your hosting provider is typically responsible for server-side software updates (like PHP, Apache, etc.), but it’s worth confirming they are up-to-date.
Secure Coding Principles
This is more relevant if you’re building a custom website or working with developers. However, understanding these concepts will help you communicate your needs effectively.
Input Validation
Always validate all data entered by users. This prevents attackers from injecting malicious code into your website through forms, search bars, or any other input field.
Output Encoding
Ensure that any data displayed on your website is properly encoded to prevent cross-site scripting (XSS) attacks, where attackers inject malicious scripts into web pages viewed by other users.
Error Handling
Avoid displaying detailed error messages to users, as these can provide attackers with valuable information about your website’s structure and vulnerabilities.
Secure Password Management: Your First Line of Defense
You might think of passwords as a basic security measure, but they are often the weakest link. Weak passwords are easy to guess or crack, giving attackers direct access to your accounts.
Strong, Unique Passwords
- Length is Key: Aim for passwords that are at least 12-16 characters long.
- Mix It Up: Combine uppercase and lowercase letters, numbers, and symbols.
- Avoid Obvious Choices: Steer clear of personal information (birthdays, pet names), common words, or sequential numbers.
- Unique Passwords for Every Account: Never reuse passwords across different platforms. If one account is compromised, others remain safe.
Password Managers: Your Digital Vault
Remembering dozens of complex, unique passwords is an impossible task. This is where password managers come in. They securely store all your passwords, allowing you to generate strong, unique passwords for each site and auto-fill them when you log in. Popular options include LastPass, 1Password, and Bitwarden.
Two-Factor Authentication (2FA): The Extra Layer
Once you have strong passwords, add a second layer of security with 2FA. This requires you to provide two different forms of identification to log in. Typically, this involves something you know (your password) and something you have (a code from your phone via an app or SMS).
Enable 2FA Everywhere Possible
Ensure 2FA is enabled for:
- Your website’s administrative access.
- Your hosting account.
- Your email accounts.
- Any other critical online services.
By focusing on these foundational elements – a reputable host, secure development practices, and robust password management – you lay a solid groundwork for a secure online presence. You’ve moved beyond just having a website to having a secure website.
Protecting Your Data: Essential Security Measures for Your Website
Now that you have a secure foundation, it’s time to implement specific measures to protect the data flowing in and out of your website and the sensitive information it stores. This is about creating robust defenses around your digital assets.
SSL/TLS Certificates: Encrypting Your Communications
You’ve likely seen the padlock icon in your browser’s address bar and the “https://” prefix. This signifies that your connection to the website is secured by an SSL/TLS certificate. This is no longer a luxury; it’s a necessity for any website that handles user data or processes transactions.
What is SSL/TLS?
SSL (Secure Sockets Layer) and its successor, TLS (Transport Layer Security), are protocols that encrypt the data exchanged between your website and your visitors’ browsers. This encryption scrambles the information, making it unreadable to anyone who might intercept it.
Why Your Business Needs an SSL Certificate
- Data Privacy and Integrity: It prevents sensitive information like login credentials, credit card numbers, and personal details from being intercepted by attackers.
- Trust and Credibility: Browsers flag websites without SSL as “not secure,” which can deter visitors and damage your brand’s reputation. Customers are more likely to trust and engage with a website that demonstrates a commitment to their security.
- SEO Benefits: Search engines like Google prioritize websites with SSL certificates, giving them a slight ranking boost.
- Compliance: Depending on your industry and the type of data you handle, an SSL certificate may be a regulatory requirement (e.g., for PCI DSS compliance if you process credit card payments).
Types of SSL Certificates
- Domain Validated (DV): The most basic type, verifying only that you own the domain. It’s suitable for most small businesses.
- Organization Validated (OV): Verifies the identity of your organization.
- Extended Validation (EV): The most rigorous form of validation, providing the highest level of trust and often displaying your organization’s name in the browser’s address bar.
How to Get an SSL Certificate
Most reputable web hosting providers offer free SSL certificates (often via Let’s Encrypt). You can also purchase certificates from Certificate Authorities (CAs). Your hosting provider or website developer can assist you with installation.
Regular Backups: Your Digital Insurance Policy
Imagine losing all your website’s content, customer data, and past sales records. It’s a catastrophic scenario, but one that can be mitigated with regular, reliable backups. Backups are your ultimate safety net.
Why Backups Are Crucial
- Disaster Recovery: In case of hardware failure, cyberattack, accidental deletion, or natural disaster, you can restore your website to a previous working state.
- Protection Against Data Loss: Human error or software glitches can lead to data corruption or loss. Backups ensure you don’t lose valuable information.
- Security Against Ransomware: If your website is infected with ransomware, a recent backup allows you to restore your site without paying the ransom.
Best Practices for Backups
- Frequency: The frequency of your backups should depend on how often your website content changes. For active sites, daily backups are recommended. For less dynamic sites, weekly might suffice, but always err on the side of more frequent.
- Storage: Store your backups off-site. This means not just on the same server as your website. Use cloud storage services (like Google Drive, Dropbox, Amazon S3) or a separate physical location.
- Testing: Periodically test your backups to ensure they are restorable. A backup that can’t be restored is useless.
- Automation: Automate your backup process to ensure consistency and prevent human oversight. Many hosting providers and website plugins offer automated backup solutions.
- Multiple Backup Copies: Consider keeping multiple backup copies (e.g., daily, weekly, monthly) for added security.
Backup Solutions for Your Website
- Hosting Provider Backups: Many hosting providers include automated backup services. Check with your provider to understand their policy and options.
- CMS Plugins: For platforms like WordPress, numerous backup plugins are available (e.g., UpdraftPlus, BackupBuddy). These plugins often offer more control over backup frequency, destination, and restoration.
- Manual Backups: While not recommended as your sole strategy, you can manually download your website files and database from your hosting control panel. Remember to store these securely off-site.
Website Firewalls (WAFs): Your Digital Gatekeeper
A Web Application Firewall (WAF) acts as a shield between your website and the internet, monitoring HTTP traffic and blocking malicious requests before they reach your server. Think of it as a bouncer at the entrance of your digital establishment.
How WAFs Work
WAFs examine incoming requests for patterns that indicate malicious activity, such as:
- SQL injection attempts.
- Cross-site scripting (XSS) attempts.
- Malicious bots.
- Exploits targeting known vulnerabilities.
They can be deployed in various ways:
- Network-Based WAFs: Hardware appliances that sit in front of your web servers.
- Host-Based WAFs: Software installed directly on your web server.
- Cloud-Based WAFs: Services provided by third-party vendors that filter traffic before it reaches your server. This is often the most accessible and effective option for small businesses.
Benefits of Using a WAF
- Protection Against Common Attacks: Prevents a wide range of known web application attacks.
- Mitigation of Zero-Day Exploits: Can help protect against emerging threats that haven’t been widely published yet.
- Improved Website Performance: By filtering out malicious traffic, a WAF can free up server resources, potentially improving website speed for legitimate users.
- Compliance Assistance: Can help meet certain security and compliance requirements.
Popular WAF Providers for Small Businesses
Many reputable security companies offer cloud-based WAF services. Cloudflare is a very popular and cost-effective option that also provides CDN (Content Delivery Network) and DDoS mitigation services. Sucuri and Wordfence are other excellent choices, particularly for WordPress users. When choosing a WAF, consider its ease of integration, the types of threats it protects against, and its pricing.
Regular Security Audits and Scans: Proactive Vulnerability Detection
Just like a physical building needs regular inspections, your website needs periodic security audits and scans to identify and address potential weaknesses before they can be exploited.
Vulnerability Scanners: Identifying Weaknesses
Vulnerability scanners are automated tools that probe your website for known security flaws. They can identify things like:
- Outdated software versions.
- Misconfigurations.
- Insecure code.
- Open ports.
These scanners can be run independently or as part of a managed security service.
Penetration Testing (Ethical Hacking): Simulating Attacks
Penetration testing, or “pen testing,” involves simulating real-world cyberattacks on your website to identify vulnerabilities. This is typically performed by security professionals who attempt to breach your defenses to expose weaknesses that automated scanners might miss. While this can be more expensive, it provides a comprehensive and realistic assessment of your security posture, especially for businesses handling highly sensitive data.
Malware Scanners: Detecting Infections
Regularly scan your website for malware. Many security plugins and services for CMS platforms include robust malware scanning capabilities. These tools can detect malicious code, backdoors, and other signs of compromise.
Importance of Professional Help
For small businesses without dedicated IT security staff, relying on automated tools and services from reputable security providers is often the most practical approach. They offer regular scans and alerts, allowing you to address issues promptly.
Implementing these measures is crucial for actively defending your website and the data it holds. You’re not just passively hoping for security; you’re actively building layers of protection to keep your business and your customers safe.
User Access and Data Privacy: Controlling Who Sees What

Beyond the technical infrastructure, controlling who has access to your website and how user data is handled is paramount. This aspect of security is about trust, permissions, and ethical data stewardship.
User Role Management: Limiting Access
If multiple people manage your website, or if you have different tiers of users (e.g., administrators, editors, subscribers), implementing effective user role management is essential.
Principle of Least Privilege
This fundamental security principle dictates that users should only have the minimum necessary permissions to perform their job functions. Granting everyone administrative access is an open invitation to disaster.
What are User Roles?
Different user roles have different levels of access and capabilities. For example:
- Administrator: Has full control over the website, can install plugins, change themes, and manage all users.
- Editor: Can publish and manage posts and pages, but cannot install plugins or themes.
- Author: Can write and publish their own posts, but cannot manage other users’ content.
- Contributor: Can write and edit their own posts, but cannot publish them without an editor’s review.
- Subscriber: Can only manage their profile.
Best Practices for User Roles
- Assign Specific Roles: Carefully assess the tasks each individual needs to perform and assign them the corresponding role.
- Regularly Review Permissions: Periodically review user roles and permissions, especially if an employee’s responsibilities change or if they leave the company.
- Delete Inactive Accounts: Promptly remove user accounts for former employees or contractors to prevent unauthorized access.
- Avoid Default Usernames: Never use default usernames like “admin.” Create unique usernames for all users.
Securely Handling Customer Data: Compliance and Trust
The data you collect from your customers is a precious resource. Protecting it not only safeguards your business but also builds trust and ensures you comply with relevant data privacy regulations.
Understanding Data Privacy Regulations
Depending on your location and the location of your customers, you may need to comply with various data privacy laws. The most well-known is the General Data Protection Regulation (GDPR) in Europe, but similar regulations exist in other regions (e.g., CCPA in California).
Key Principles of Data Privacy
- Consent: You must obtain explicit consent from users before collecting and processing their personal data.
- Transparency: You should clearly inform users about what data you collect, why you collect it, and how you use it.
- Data Minimization: Only collect the data that is absolutely necessary for your stated purpose.
- Purpose Limitation: Use collected data only for the specific purposes for which consent was obtained.
- Data Security: Implement appropriate technical and organizational measures to protect personal data.
Implementing a Privacy Policy
A clear and comprehensive privacy policy is a legal requirement in many jurisdictions and a vital component of building customer trust. Your privacy policy should outline:
- What types of personal data you collect.
- How you collect this data.
- The purpose for which you collect and use the data.
- Who you share the data with (if anyone).
- How users can access, modify, or delete their data.
- Your contact information.
Make your privacy policy easily accessible from your website.
Secure Payment Processing
If your website accepts payments online, security is paramount. You must comply with Payment Card Industry Data Security Standard (PCI DSS) if you handle credit card information.
PCI DSS Compliance
PCI DSS is a set of security standards designed to ensure that all companies that accept, process, store, or transmit credit card information maintain a secure environment.
- Do Not Store Sensitive Cardholder Data: Whenever possible, avoid storing full credit card numbers on your servers. Use trusted third-party payment gateways that handle the sensitive data directly and provide you with transaction tokens.
- Use Secure Payment Gateways: Integrate with reputable payment gateways like Stripe, PayPal, Square, or authorize.net. These services are designed with PCI DSS compliance in mind.
- Regular Security Audits: Even when using third-party gateways, ensure your own website and systems are secure and regularly audited.
Securely Storing Passwords and Sensitive Data
If you must store user passwords, always hash and salt them. Hashing is a one-way encryption process, and salting adds a unique random string to each password before hashing, making it much harder for attackers to crack even if they obtain a database of hashed passwords. Avoid storing unencrypted sensitive data like credit card numbers or social security numbers at all costs.
By diligently managing user access and prioritizing data privacy, you demonstrate a commitment to your customers’ security and build a reputation as a trustworthy business. These practices go beyond technical fixes; they are about fostering an ethical and secure environment for your online operations.
For small business owners looking to enhance their online presence, understanding website security is crucial. A great resource that complements the Small Business Website Security Guide for Beginners is an article that discusses the latest website security best practices in 2023. By following these guidelines, you can better protect your site from potential threats and ensure a safer experience for your customers. To explore these essential practices, check out the article here.
Ongoing Vigilance: The Continuous Nature of Website Security
| Security Measure | Description |
|---|---|
| SSL Certificate | Encrypts data transmitted between the website and its visitors |
| Strong Passwords | Encourages the use of complex and unique passwords for website access |
| Regular Updates | Keeps website software, plugins, and themes up to date to patch security vulnerabilities |
| Firewall Protection | Blocks malicious traffic and unauthorized access attempts |
| Backup System | Regularly backs up website data to prevent data loss in case of security breach |
Website security is not a one-time task; it’s an ongoing commitment. The threat landscape is constantly evolving, and attackers are always developing new methods. Therefore, continuous vigilance and proactive adaptation are crucial to maintaining a secure website.
Monitoring Your Website: Staying Alert
Regularly monitoring your website for suspicious activity is vital. This proactive approach allows you to detect potential issues before they escalate into major breaches.
Website Uptime Monitoring
As mentioned earlier, DDoS attacks can render your website inaccessible. Uptime monitoring tools can alert you immediately if your website goes offline, allowing you to investigate the cause and take corrective action.
Security Logging and Analysis
Most web servers and security tools generate logs that record various events, including login attempts, file access, and error messages. Regularly reviewing these logs can help you identify patterns of suspicious activity, such as a surge in failed login attempts or unusual traffic patterns. While manual log analysis can be daunting, many security services offer automated log analysis and alerting.
User Activity Monitoring
If you have multiple users with access to your website, monitoring their activity can help detect unauthorized actions or misuse of credentials. This can be achieved through your CMS’s built-in audit logs or dedicated security plugins.
Keeping an Eye on Software Updates
We’ve emphasized this repeatedly, but it bears reiteration. Actively monitor for new updates for your CMS, plugins, themes, and any other software your website relies on. Set up automatic notifications or subscribe to developer newsletters for timely alerts.
Incident Response Plan: What to Do When Things Go Wrong
Even with the best preventative measures, a security incident can still occur. Having a well-defined incident response plan in place is essential for minimizing damage and recovering quickly.
Components of an Incident Response Plan
- Identify the Incident: Clearly define what constitutes a security incident for your business.
- Containment: Outline the steps to take to prevent the incident from spreading or causing further damage. This might include taking the website offline or disabling certain functionalities.
- Eradication: Detail the process of removing the threat, such as removing malware or patching vulnerabilities.
- Recovery: Describe how to restore your website and data to normal operations.
- Post-Incident Analysis: Explain how you will analyze the incident to understand its root cause and prevent future occurrences.
- Communication Plan: Outline who needs to be notified (e.g., customers, legal counsel, regulatory bodies) and how those communications will be handled.
Practicing Your Plan
An incident response plan is only effective if it’s understood and practiced. Conduct tabletop exercises with your team to walk through various scenarios and ensure everyone knows their role.
Staying Informed About Emerging Threats
The cybersecurity landscape is dynamic. To stay ahead of threats, you need to stay informed about the latest trends, vulnerabilities, and best practices.
Follow Reputable Security Sources
Subscribe to newsletters from cybersecurity firms, follow security experts on social media, and read industry blogs and news outlets that cover cybersecurity.
Cybersecurity Training
Invest in cybersecurity training for yourself and any employees who manage your website. This doesn’t need to be overly technical; basic awareness of phishing tactics, password hygiene, and social engineering can significantly improve your overall security posture.
Regular Security Reviews
Schedule regular intervals (e.g., quarterly or annually) to conduct a comprehensive review of your website’s security. This might involve revisiting your hosting plan, evaluating your WAF’s effectiveness, and updating your incident response plan.
By embracing continuous vigilance, you transform website security from a daunting chore into an integrated, proactive part of your business operations. You are no longer just reacting to threats; you are actively building a resilient and secure digital environment for your small business and the customers you serve. You’ve taken the essential steps to protect your online presence, ensuring that your digital storefront remains open, secure, and trustworthy for years to come.
FAQs
1. Why is website security important for small businesses?
Website security is important for small businesses because it helps protect sensitive customer information, such as payment details and personal data, from being compromised. A secure website also helps build trust with customers and can prevent costly data breaches and legal issues.
2. What are some common website security threats that small businesses should be aware of?
Common website security threats include malware, phishing attacks, DDoS (Distributed Denial of Service) attacks, and SQL injection. These threats can lead to data theft, website downtime, and damage to a small business’s reputation.
3. What are some basic steps small businesses can take to improve website security?
Small businesses can improve website security by using strong, unique passwords, keeping software and plugins up to date, using HTTPS encryption, implementing a web application firewall, and regularly backing up website data.
4. How can small businesses protect customer data on their websites?
Small businesses can protect customer data on their websites by using secure payment gateways, encrypting sensitive information, implementing access controls, and complying with data protection regulations such as GDPR and CCPA.
5. What should small businesses do if they suspect a security breach on their website?
If a small business suspects a security breach on their website, they should immediately take the website offline, investigate the breach, notify affected customers, and work with a cybersecurity professional to address the issue and prevent future breaches.










Add comment