We live in an interconnected world where our digital identities are as crucial as our physical ones. Among these, our domain names stand as the gateways to our online presence, representing our businesses, brands, and personal endeavors. The thought of losing control over such a vital asset – through domain hijacking – is enough to send shivers down our spines. Domain hijacking, at its core, is the unauthorized transfer or modification of a domain’s registration. It’s a hostile takeover that can lead to devastating consequences: loss of revenue, reputational damage, data breaches, and a complete disruption of our online operations. As responsible digital citizens and stewards of our online properties, we must proactively secure our domains. This article will delve into the best practices we can adopt to prevent domain hijacking, ensuring our digital fortresses remain impregnable.
Before we can effectively defend ourselves, we need a clear understanding of the threats we face. Domain hijacking isn’t a single, uniform attack; it encompasses a range of methods attackers employ to seize control of our valuable online real estate. By dissecting these common vectors, we can better identify our vulnerabilities and build robust defenses.
Social Engineering: The Human Element as a Weak Link
We often underestimate the power of human manipulation, but social engineering remains one of the most potent tools in a hijacker’s arsenal. Attackers exploit our trust, our busy schedules, and our inherent desire to be helpful to gain access to critical information or trick us into performing actions that compromise our domains.
- Phishing and Spear Phishing: We’ve all seen them – those seemingly legitimate emails or messages that urge us to click a link or provide our login credentials. Phishing campaigns, especially when targeted (spear phishing), can be incredibly convincing. They often mimic legitimate communications from our domain registrars, web hosting providers, or even internal IT departments. If we fall for these sophisticated traps, we unknowingly hand over the keys to our domain.
- Vishing (Voice Phishing) and Smishing (SMS Phishing): Beyond email, attackers also leverage phone calls and text messages. A convincing caller might pose as a registrar support agent, claiming an issue with our account and requesting verification details. Similarly, SMS messages can contain malicious links or requests for sensitive information. We must always be wary of unsolicited communications, regardless of the medium.
- Tailgating and Pretexting: While less common for purely domain-related attacks, these on-site social engineering tactics can still indirectly contribute to domain compromise. An attacker might gain physical access to our office, observe us typing passwords, or impersonate a legitimate service provider to glean information that facilitates a later digital attack. We mustn’t solely focus on digital defenses; physical security also plays a role in our overall posture.
Exploiting Technical Vulnerabilities: Cracks in Our Digital Armor
Beyond human deception, attackers also seek out and exploit weaknesses in the systems and software we use to manage our domains. These technical vulnerabilities can range from insecure configurations to outdated software.
- Weak Passwords and Credential Stuffing: This is perhaps the most fundamental vulnerability. If we use weak, easily guessed passwords or reuse passwords across multiple services, we’re inviting trouble. Credential stuffing attacks, where attackers take lists of compromised credentials from data breaches and try them against various services (including domain registrars), are alarmingly common. We must prioritize strong, unique passwords for all our online accounts, especially those tied to our domain.
- DNS Manipulation: The Domain Name System (DNS) is the internet’s phonebook, translating human-readable domain names into IP addresses. If an attacker gains control of our DNS records, they can redirect our website traffic to their malicious servers, effectively taking our site hostage. This can happen through unauthorized access to our registrar account or by compromising our DNS hosting provider.
- Expired Domain Registrations: While not strictly “hijacking” in the malicious sense, allowing our domain registration to expire can lead to its eventual loss. If we fail to renew our domain within the grace period, it can be put up for auction or eventually registered by someone else. Attackers often monitor expired domain lists, looking for valuable domains to snap up.
- Software Vulnerabilities (Registrar/Hosting Provider): Even if we follow all best practices, our domain could still be at risk if our registrar or hosting provider has security vulnerabilities in their systems. While we can’t directly control their security posture, we must choose reputable providers with a strong track record of security and quick patching.
Insider Threats: The Risk from Within
It’s an uncomfortable truth, but sometimes the threat comes from within our own organizations. Disgruntled employees, former staff, or even contractors with privileged access can intentionally or unintentionally compromise our domain.
- Disgruntled Employees: Individuals with grudge against the company, or those seeking financial gain, can exploit their access to damage the organization. This could involve changing DNS records, transferring the domain, or even just deleting critical information.
- Negligent Employees: Sometimes, employees with good intentions but lacking proper security awareness can inadvertently expose our domain to risk. They might fall for a phishing scam, share credentials, or fail to follow established security protocols.
- Former Employees with Unrevoked Access: A common oversight for businesses is failing to revoke access credentials for departed employees. An ex-employee with continued access to the domain registrar or DNS management could become an unintentional or intentional threat.
Understanding these multifaceted threats is the first step towards building a comprehensive defense strategy. Now, let’s explore the actionable best practices we can implement.
To enhance your understanding of domain security best practices and prevent hijacking, you may find it beneficial to explore related insights on how effective business hosting can significantly boost your online sales and revenue. This article discusses the importance of a secure hosting environment and its role in protecting your online assets. For more information, visit this article.
Building a Strong Foundation: Registrar and Account Security
Our domain registrar is the ultimate gatekeeper of our domain. Securing our account with them is paramount. This involves not just strong passwords but a multi-layered approach to access control and information accuracy.
Choosing Wisely: Selecting a Reputable Registrar
The security journey begins with our choice of domain registrar. Not all registrars are created equal, and we must prioritize security when making this critical decision.
- Accreditation and Reputation: We should always choose ICANN-accredited registrars with a long-standing positive reputation for security and customer service. Look for independent reviews and industry recognition. A registrar that has experienced significant security breaches in the past, or one with a history of poor support, should raise red flags.
- Security Features Offered: We need to scrutinize the security features our chosen registrar provides. Do they offer two-factor authentication (2FA)? Do they provide domain locking? What are their protocols for account recovery after a suspected breach? A robust suite of security features is non-negotiable.
- Transparency and Communication: A good registrar will be transparent about their security practices and communicate proactively about any potential threats or system updates. We want a partner who takes security seriously and keeps us informed.
Fortifying Our Account: Multi-Factor Authentication (MFA) is Key
If there’s one single most effective measure we can take to protect our registrar account, it’s enabling Multi-Factor Authentication (MFA). We cannot stress this enough.
- Beyond Passwords: MFA adds an extra layer of security beyond just a password. Even if an attacker manages to steal our password, they won’t be able to log in without the second factor (e.g., a code from our phone, a biometric scan, or a hardware token).
- Types of MFA: We should utilize the strongest forms of MFA available. Hardware security keys (like YubiKey) offer the highest level of protection. Authenticator apps (Google Authenticator, Authy) are also excellent choices. SMS-based MFA, while better than nothing, is considered less secure due to potential SIM swap attacks.
- Mandate MFA for All Users: If multiple individuals within our organization have access to the registrar account, we must mandate MFA for every single one of them. A single compromised account can undermine all our efforts.
The Power of Strong and Unique Passwords
While MFA adds an extra layer, strong and unique passwords remain the foundational element of account security.
- Complexity and Length: We should employ passwords that are long (at least 12-16 characters) and combine uppercase and lowercase letters, numbers, and special characters. Avoid easily guessable information like names, birthdays, or common dictionary words.
- Password Managers: We strongly recommend using a reputable password manager. These tools generate strong, unique passwords for each of our online accounts and store them securely, eliminating the need for us to remember them all. This is crucial for preventing credential stuffing attacks.
- Avoid Reuse: Never, ever reuse passwords across multiple services. If one service is breached, every other service using that same password becomes vulnerable.
Protecting Our Domain’s Vulnerable Points: DNS and Contact Information
Our domain’s security isn’t just about the registrar account; it extends to the integrity of our DNS records and the accuracy of our contact information. Attackers exploit weaknesses in these areas to hijack our online presence.
Securing Our DNS: The Internet’s Phonebook
Our DNS records dictate where our domain points on the internet. Compromising these records can lead to our website being redirected, emails being intercepted, and a complete disruption of our online services.
- DNSSEC (Domain Name System Security Extensions): We must enable DNSSEC for our domains. DNSSEC adds a layer of cryptographic security to the DNS, protecting against cache poisoning and other forms of DNS manipulation. It ensures that when a user requests our domain, they are directed to the authentic server, not a malicious one. Many registrars and DNS providers offer DNSSEC; we just need to enable it.
- Locked Domain Records: Most registrars offer a “domain lock” or “registrar lock” feature. This prevents unauthorized transfers or modifications to our domain’s WHOIS information and DNS settings without manual intervention. We should always have this feature enabled. It acts as an important barrier against quick, unauthorized changes.
- Secure DNS Provider: If we’re using a third-party DNS provider (e.g., Cloudflare, Amazon Route 53), we must ensure they also have robust security measures in place, including MFA for our account with them and a strong track record of preventing DNS attacks.
Accurate and Private WHOIS Information
The WHOIS database contains public information about our domain registration, including contact details. While often seen as a formality, it’s a critical component of our security.
- Keep Contact Information Up-to-Date: We need to ensure that the administrative, technical, and billing contact information associated with our domain is always accurate and current. If a hijacker manages to initiate a domain transfer, the registrar will typically send notifications to these contacts. If the information is outdated, we might miss these crucial alerts.
- Leverage WHOIS Privacy Protection: For individual domain owners or small businesses, we might consider using WHOIS privacy protection (also known as private registration). This service masks our personal contact information from public view in the WHOIS database, replacing it with the registrar’s details. This helps to prevent social engineering attacks where hijackers harvest personal information from WHOIS records to craft convincing phishing attempts. While there are some debates around transparency, the security benefits for many outweigh the drawbacks.
- Monitor WHOIS Changes: We should periodically review our domain’s WHOIS record to ensure no unauthorized changes have been made. Many services can alert us if changes are detected, which can be an early warning sign of a potential hijacking attempt.
Vigilance and Preparation: Monitoring and Incident Response

Preventing domain hijacking isn’t a one-and-done task; it requires ongoing vigilance and a prepared response plan. Even with the best defenses, a determined attacker might find a way in. Our ability to detect, react, and recover quickly is paramount.
Constant Monitoring and Alert Systems
We need to actively monitor our domain for any suspicious activity. Passive defense is not enough; proactive surveillance is key.
- Registrar Notifications: We should ensure that email addresses and phone numbers associated with our registrar account are regularly checked and belong to trusted individuals, preferably more than one. These contact points will receive critical alerts about domain changes, renewals, and transfer requests.
- Domain Monitoring Services: There are various third-party services that can monitor our domain for us, alerting us to changes in DNS records, WHOIS information, SSL certificate status, and even domain registrar details. These services act as an early warning system, notifying us of unauthorized modifications before they escalate.
- Website Uptime Monitors: While not directly for domain hijacking, an unexpected downtime alert from our website monitoring service can be an indicator that something is amiss, potentially related to DNS changes or server redirection, which are common results of a successful domain hijack.
Developing an Incident Response Plan
Hope for the best, prepare for the worst. A well-defined incident response plan can significantly reduce the damage and recovery time in the event of a domain hijack.
- Designate a Core Team: We need to identify individuals who will be responsible for responding to a potential domain hijacking event. This team should include representatives from IT, legal, communications, and senior management.
- Establish Communication Channels: How will the team communicate if normal channels (like email hosted on the compromised domain) are down? We need backup communication methods (e.g., dedicated secure messaging apps, out-of-band email addresses).
- Clear Chain of Command and Procedures: What are the immediate steps to take? Who needs to be contacted internally and externally (registrar, law enforcement, affected customers)? We need clear, documented procedures for identifying, containing, eradicating, and recovering from a domain hijack.
- Backup and Recovery: While not directly preventing hijacking, having robust backups of our website data and configurations is crucial for a swift recovery if our domain is compromised and content is altered or deleted.
- Legal Counsel and Law Enforcement: We should have contact information for legal counsel experienced in cybercrime and local law enforcement agencies that handle digital theft. Time is of the essence in these situations.
To enhance your understanding of domain security best practices and how to prevent hijacking, you might find it beneficial to explore related strategies in local SEO. For instance, the article on local SEO for Pakistani businesses discusses how securing your online presence can improve your visibility and protect your brand from potential threats. By implementing robust security measures, you not only safeguard your domain but also boost your chances of ranking higher in search results.
Educating Our Team: Human Firewall Against Social Engineering
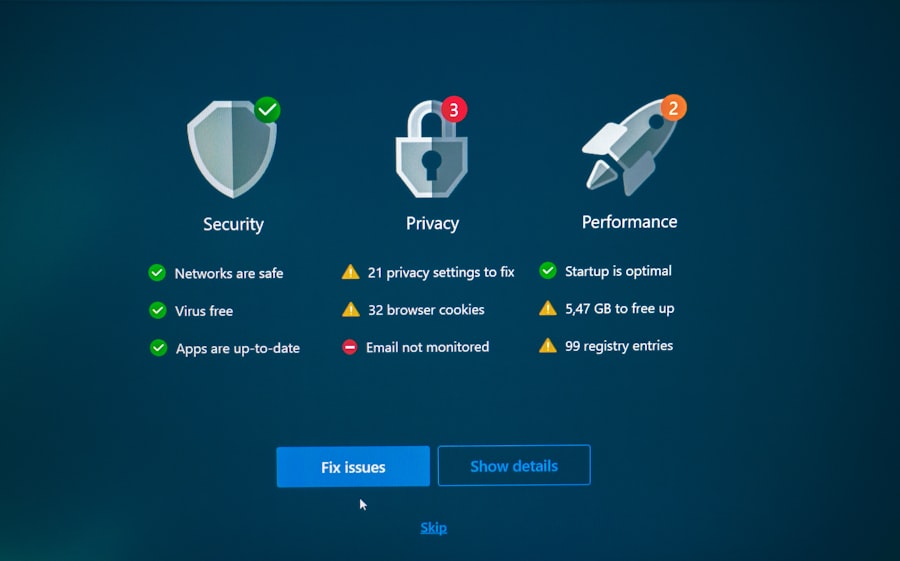
| Best Practice | Description |
|---|---|
| Use strong passwords | Ensure that domain accounts have strong, unique passwords to prevent unauthorized access. |
| Enable two-factor authentication | Implement two-factor authentication to add an extra layer of security for domain access. |
| Regularly update software | Keep domain software and systems up to date to patch any security vulnerabilities. |
| Monitor domain activity | Regularly monitor domain activity for any suspicious behavior or unauthorized changes. |
| Use DNSSEC | Implement DNS Security Extensions (DNSSEC) to add an extra layer of security to domain name system. |
Technology alone cannot completely secure us. Our employees, colleagues, and anyone with access to our domain-related accounts are the first and often last line of defense. Investing in security awareness training is an investment in our overall security.
Regular Security Awareness Training
Ignorance is not bliss when it comes to cybersecurity. We must empower our team with the knowledge and skills to identify and respond to threats.
- Recognizing Phishing and Social Engineering: We need to educate our team on the tell-tale signs of phishing emails, malicious websites, and social engineering tactics. Regular simulated phishing exercises can be invaluable in training them to spot and report suspicious activity.
- Strong Password Practices: Reinforce the importance of strong, unique passwords and the use of password managers. Conduct regular refreshers on password best practices.
- MFA Usage and Importance: Ensure everyone understands how to use MFA and why it’s a critical security measure. Address any complacency or attempts to bypass it.
- Reporting Suspicious Activity: We need to foster a culture where employees feel comfortable and empowered to report anything that seems out of place, even if they’re not 100% sure it’s a threat. Early reporting can be crucial.
Strict Access Control and Least Privilege Principles
Not everyone needs access to everything. Implementing the principle of least privilege is fundamental to minimizing our attack surface.
- Role-Based Access: We should grant access to our domain registrar and DNS management only to those who absolutely require it for their job functions. We should define specific roles and assign appropriate permissions based on those roles.
- Regular Access Reviews: Periodically review who has access to our critical domain management systems. Remove access for employees who no longer need it (e.g., those who have changed roles or left the company).
- Dedicated Accounts and Audit Trails: Avoid sharing generic login credentials. Each individual with access should have their own unique account, allowing for clear audit trails of who did what and when. This accountability is vital for identifying the source of any unauthorized changes.
- Vendor and Third-Party Access: If we rely on external agencies or freelancers to manage our website or DNS, we must scrutinize their security practices and limit their access to only what is strictly necessary for their tasks. Ensure contracts include data security clauses.
In closing, securing our domain is an ongoing commitment, not a one-time setup. By understanding the threats, implementing robust technical safeguards, maintaining diligent oversight, and empowering our team with knowledge, we can significantly reduce the risk of falling victim to domain hijacking. Our digital presence is invaluable, and protecting it is a responsibility we must take seriously. Through these best practices, we can build a resilient digital infrastructure that stands firm against the evolving landscape of cyber threats.
FAQs
What is domain hijacking?
Domain hijacking is the unauthorized transfer of a domain name to another party without the permission of the original registrant. This can occur through various means such as hacking into the domain registrar’s account or exploiting security vulnerabilities.
What are some best practices to prevent domain hijacking?
Some best practices to prevent domain hijacking include enabling two-factor authentication for domain registrar accounts, regularly updating and strengthening account passwords, using domain locking features provided by registrars, and monitoring domain registration and expiration dates.
How can DNSSEC help prevent domain hijacking?
DNSSEC (Domain Name System Security Extensions) is a set of security protocols designed to add an additional layer of authentication and integrity to the domain name system. By implementing DNSSEC, domain owners can help prevent unauthorized changes to their domain’s DNS records, reducing the risk of domain hijacking.
What should I do if my domain is hijacked?
If you suspect that your domain has been hijacked, you should immediately contact your domain registrar to report the issue. They can assist you in regaining control of your domain and investigating the unauthorized transfer. It’s also important to review your account security and take steps to prevent future hijacking attempts.
Are there any legal measures to protect against domain hijacking?
Yes, there are legal measures that can be taken to protect against domain hijacking. These may include registering trademarks related to your domain name, implementing domain name monitoring services, and pursuing legal action against individuals or entities involved in unauthorized domain transfers. It’s important to consult with legal professionals to understand the options available in your specific situation.










Add comment